A security engineer focusing on fuzzers, exploits, and mitigations for Linux and Android kernels.
-
🪓 Exploiting the Linux Kernel [4 days]

A 4-day Linux kernel exploitation frenzy!
This training guides researchers through the field of Linux kernel exploitation. In a series of practical labs, the training explores the process of exploiting kernel bugs in a modern Linux distribution on the x86-64 architecture.
The training starts with the beginner topics but proceeds into advanced areas as well. The beginner chapters include learning the techniques to escalate privileges and bypass foundational mitigations in x86-64 kernels. The advanced chapters are dedicated to slab (heap) exploitation, including an in-depth analysis of the kernel allocators’ internals.
-
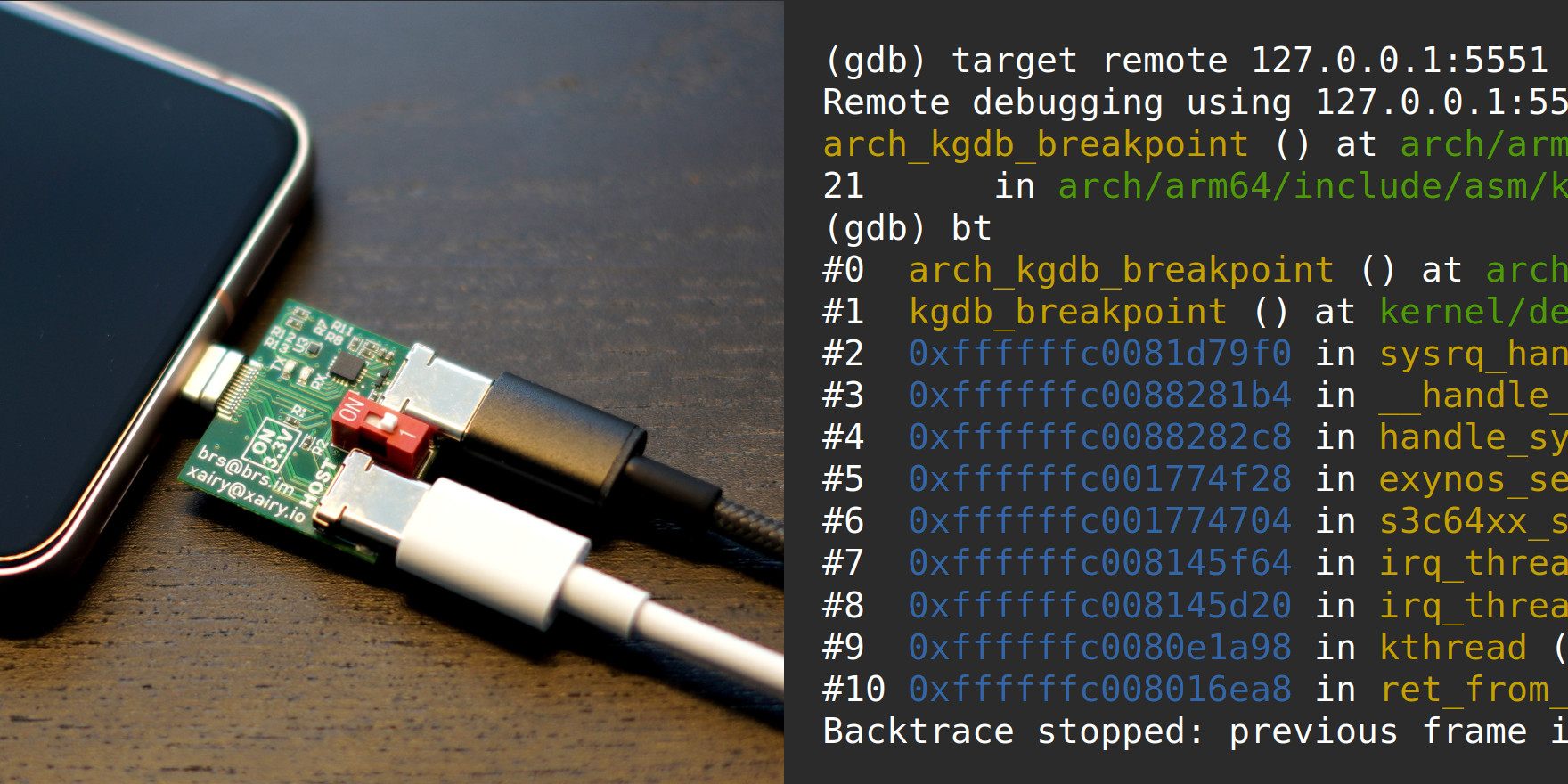
📲 Debugging the Pixel 8 kernel via KGDB
This article shows how to use GDB over a serial connection for debugging the kernel on a Pixel 8.
The instructions cover building and flashing a custom Pixel 8 kernel to enable KGDB, breaking into KGDB either via ADB by relying on
/proc/sysrq-triggeror purely over a serial connection by sending the SysRq-G sequence, and attaching GDB to the Pixel 8 kernel.The instructions should be adaptable to other Pixels as well.
-
🧱 SLUB Internals for Exploit Developers

A talk that covers the SLUB allocator internals and explains how common Slab shaping approaches work for exploiting Slab memory corruption bugs.
-
🥥 Linux Kernel Security channel

A Telegram channel about Linux kernel security. Me and Alexander Popov regularly post links to materials about exploits, fuzzers, mitigations, and other security-related things there.
The posts are also mirrored on X, Bluesky, Mastodon, and Reddit.